- Home
- Articles
- Architectural Portfolio
- Architectral Presentation
- Inspirational Stories
- Architecture News
- Visualization
- BIM Industry
- Facade Design
- Parametric Design
- Career
- Landscape Architecture
- Construction
- Artificial Intelligence
- Sketching
- Design Softwares
- Diagrams
- Writing
- Architectural Tips
- Sustainability
- Courses
- Concept
- Technology
- History & Heritage
- Future of Architecture
- Guides & How-To
- Art & Culture
- Projects
- Competitions
- Jobs
- Events
- Store
- Tools
- More
- Home
- Articles
- Architectural Portfolio
- Architectral Presentation
- Inspirational Stories
- Architecture News
- Visualization
- BIM Industry
- Facade Design
- Parametric Design
- Career
- Landscape Architecture
- Construction
- Artificial Intelligence
- Sketching
- Design Softwares
- Diagrams
- Writing
- Architectural Tips
- Sustainability
- Courses
- Concept
- Technology
- History & Heritage
- Future of Architecture
- Guides & How-To
- Art & Culture
- Projects
- Competitions
- Jobs
- Events
- Store
- Tools
- More
Privacy by Design: Rethinking Control in Digital Environments

Table of Contents Show
Digital environments are no longer just functional systems. They are layered structures where data, interaction, and access define how users experience space. As more activity moves online, the architecture of these systems becomes increasingly important not only in terms of performance, but in how they handle control.
In this context, privacy is no longer a secondary feature. It is part of the structure itself. The way a system is designed determines who can see information, who can act on it, and how much control a user retains. This shifts privacy from a setting that can be adjusted to a core design decision that shapes the entire environment.
Why Privacy Has Become a Design Problem
For a long time, privacy was treated as an additional layer – something users could manage through settings or permissions. This approach assumed that the underlying system would remain the same, while users adjusted how much of themselves they exposed.
Today, that assumption no longer holds. Digital systems are built around data. Every interaction generates information, and that information is often stored, processed, and shared across platforms. In such an environment, privacy cannot be separated from the system itself.
As a result, privacy becomes a design problem. It requires decisions about structure, access, and visibility at the architectural level. Designers and developers are not only shaping how systems look and function, but also how they handle control. The question is no longer whether users can manage their privacy, but whether the system allows them to do so in a meaningful way.
Digital Infrastructure and the Question of Control
At the core of any digital system is a question of control: who defines access, who manages data, and who ultimately decides how information is used. In centralized environments, these decisions are typically made by the platform itself. Users interact with the system, but the structure behind it determines what is visible, what can be changed, and how interactions are recorded.
This model has practical advantages, but it also creates limitations. When control is concentrated, users depend on the rules and stability of a single system. Access can be modified, restricted, or removed, and transparency is often shaped by what the platform chooses to expose.
Decentralized approaches introduce a different model. Instead of relying on a single authority, control is distributed across a network. This changes how access is defined and how data is handled. The structure becomes less about centralized management and more about shared rules that are applied consistently across participants.
How Privacy Is Implemented in Decentralized Systems
Not all decentralized systems treat privacy in the same way. Some prioritize transparency, making transactions and interactions visible by design. This can support accountability, but it also raises questions about how much information should be exposed.
Transparency vs Privacy
There is an inherent tension between transparency and privacy. Systems that make all activity visible can be easier to verify, but they can also reveal more than users intend to share. On the other hand, systems that prioritize privacy limit visibility, which can protect users but reduce external insight.
Designing around this balance requires careful decisions. It is not simply a matter of choosing one over the other, but of defining how much exposure is necessary for the system to function while preserving user control.
Privacy-Focused Networks
Some networks take a different approach by embedding privacy directly into their structure. Instead of making all interactions visible, they are designed to minimize the amount of information that is exposed during transactions.
In these systems, privacy is not an optional feature. It is part of how the network operates. This shifts the focus from managing visibility after the fact to controlling what is revealed in the first place.
The Role of Tools in Maintaining Privacy
Even when privacy is built into the underlying system, it does not exist in isolation. Users still need a way to interact with that system, and the design of this interaction layer determines how effectively privacy is preserved in practice. Without the right tools, even well-designed infrastructure can become difficult to use or misunderstand.
To manage private transactions and maintain control, users rely on an xmr wallet that acts as the interface between them and the network. It is through this interface that actions are approved, information is shared, and access is managed. The quality of this layer directly affects how much control a user can realistically maintain.
Access and Control Through Interfaces
Interfaces shape how users experience control. A wallet, for example, brings together different actions: viewing balances, confirming transactions, managing access into a single environment. This consolidation makes it easier to understand what is happening and to make informed decisions.
Control, in this sense, is not just about ownership. It is about clarity. When users can see what they are approving and how their data is being handled, they are better positioned to manage their interactions within the system.
Interaction Without Exposure
Privacy-focused systems aim to reduce unnecessary exposure, but this depends on how interactions are designed. Each action whether sending assets or confirming a transaction has the potential to reveal information.
Well-designed tools minimize this exposure. They allow users to complete actions without sharing more data than necessary. This approach aligns with the idea of privacy by design, where control is embedded into every interaction rather than added afterward.

Designing Systems That Respect User Control
Designing for privacy requires more than adding protective features. It involves rethinking how systems are structured from the beginning. Control should not be something users have to recover – it should be something they retain by default.
This shifts responsibility toward those who design and build digital environments. Decisions about data flow, visibility, and access define how much control users actually have. When these decisions prioritize user autonomy, systems become more resilient and more aligned with long-term trust.
Respecting user control also means reducing unnecessary dependence on centralized points of authority. When users can interact with systems without relying entirely on a single intermediary, they gain flexibility and independence. This does not eliminate complexity, but it redistributes it in a way that gives users a more active role.
A Shift Toward Privacy-Aware Digital Architecture
As digital systems continue to evolve, privacy is moving from the margins into the core of design thinking. It is no longer treated as an optional layer that can be adjusted after a system is built. Instead, it becomes part of the structure itself, influencing how interactions are defined and how data flows through an environment.
This shift reflects a broader change in how digital architecture is understood. Systems are not only evaluated by performance or usability, but also by how they handle control. The ability to limit exposure, manage access, and maintain autonomy becomes a key part of what makes a system effective.
In this context, infrastructure and interface are closely connected. Privacy-focused networks provide the foundation, but tools such as wallets determine how that foundation is experienced. Together, they shape an environment where users can interact without giving up control by default.
Over time, this approach points toward a more balanced model of digital interaction – one where functionality and privacy are not in conflict, but designed to work together.
illustrarch is your daily dose of architecture. Leading community designed for all lovers of illustration and drawing.
Submit your architectural projects
Follow these steps for submission your project. Submission FormLatest Posts
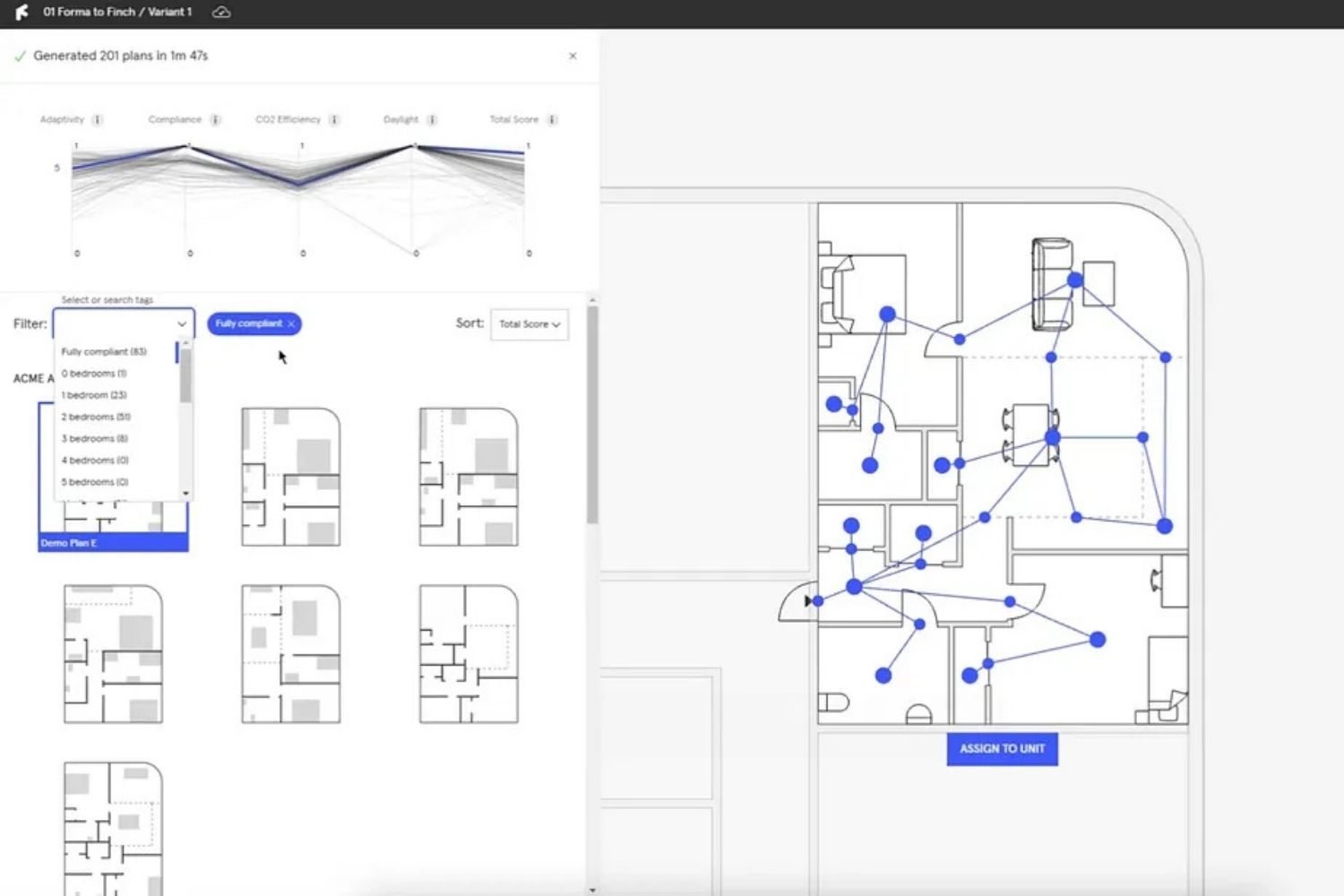
Finch3D Review 2026: How Generative AI Is Changing Early-Stage Architectural Design
This Finch3D review covers how the Swedish-built generative design platform helps architects...
Notion vs Trello vs Monday: Best Project Management Tools for Architecture Firms
A focused comparison of Notion, Trello, and Monday for architects and design...
Golden Ratio First Used in Architecture: A Complete Historical Timeline
From the Great Pyramid of Giza to the Parthenon and Le Corbusier's...
What’s The Most Popular Bathroom Vanity Color? How to Choose?
Table of Contents Show Why This Choice Matters More Than You ThinkThe...







Leave a comment